Server shut down
Who is behind the ransom hackers Darkside?

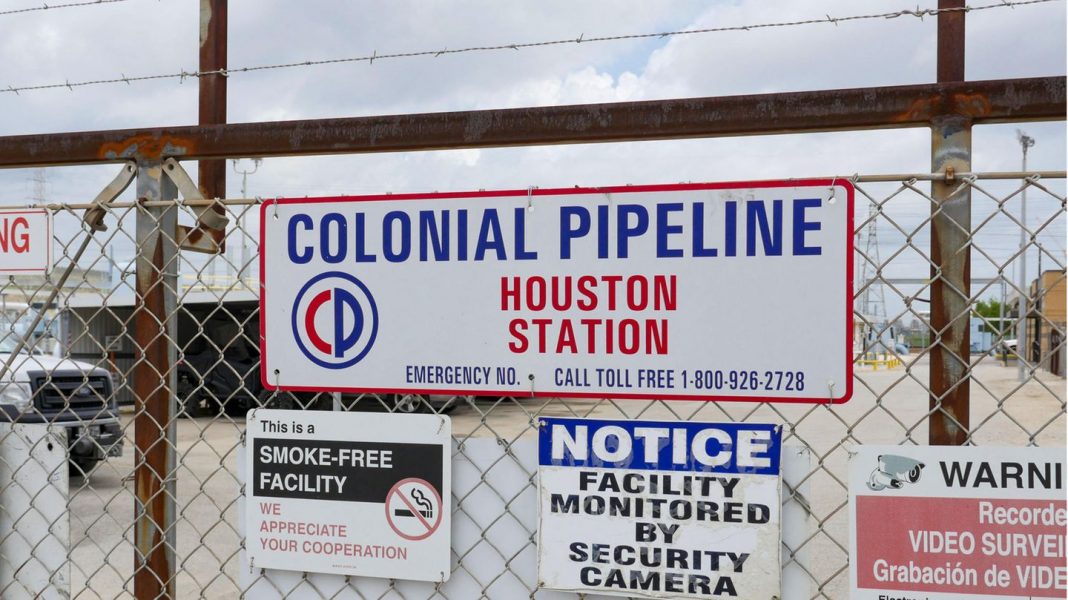
After the hacker attack on one of the most important fuel pipelines in the US, gasoline is running low in the southeast of the country. According to data provider GasBuddy, 65 percent of gas stations in the state of North Carolina and 43 percent in Georgia reported empty gas pumps on Wednesday. In the city of Atlanta, the rate was just under 60 percent. A customer at a gas station in Sandy Springs, Georgia, on Wednesday: “I came here about 15-20 minutes ago. This hacker attack on the Colonial Pipeline has probably led to the fact that there is currently no fuel coming to Atlanta. So I try to refuel now before I run out of gas so I can continue to work.”The average price of gasoline in the United States rose on Wednesday to three dollars per gallon (just under 0.66 euros per liter), as the American Automobile Association announced. This was the highest level since October 2014. About a week earlier, a hacker attack had paralyzed the lines of Colonial Pipeline. Through it flows almost half of the fuel supply of the US East Coast. The alleged responsible party, a hacker group called “DarkSide”, has stated that their motive is financial gain and not political. Colonial did not initially know how far the efforts to restore the pipeline had progressed.
A pipeline operator in the US and the Irish health authority were probably attacked within a week with malware from the same mysterious hacker group: Darkside. Apparently, the server has now been shut down.
A week after the cyber-attack on a U.S. Pipeline, the Irish health authority has become the target of a similar attack. “There is a significant ransomware attack on the IT systems,” the agency said on Twitter. According to initial findings, both hacker attacks are blamed on international criminals. This is known about the group Darkside:
- A relatively new grouping
According to experts, Darkside first appeared in August 2020. It is one of an increasing number of groups that do not actively attack themselves, but rather provide extortion software for other criminals-and then collect a share of the ransom.
Darkside specializes in so – called ransomware, the name goes back to the English word “ransom” – meaning ransom: hackers try to use malicious programs to lock or encrypt computer systems, and extort money from users for the release of the data.
The US Federal Police (FBI) firmly believes that Darkside software was behind the attack on the largest pipeline in the US a week ago. And in the cyber attack on the Irish health authority on Friday, according to initial findings, ransomware similar to the hacker attack on the US pipeline operator Colonial was used.
Experts assume that the team behind Darkside consists of very experienced hackers. The software is significantly further developed than previous versions of extortion Trojans. “Darkside software uses the double blackmail strategy: the attackers do not only encrypt the user’s data. Rather, they withdraw all information beforehand and threaten to publish it if the ransom is not paid, ” say analysts at Cybereason, a company that seeks to protect companies against such attacks.
Double strategy leverages precautions
According to Cybereason, this double strategy undermines the precaution that many companies have taken so far, which keeps their data back in a backup for fear of encryption or blocking by hackers in another location. By stripping Darkside software of the data prior to encryption, the attackers could not only demand money for unlocking the data, but also threaten to publish or sell the information to competitors.
“The amount of Darkside ransom is between 200,000 and two million dollars,” estimated the National Cybersecurity Agency in France (Ansii) in February. But it was probably still too low: According to Bloomberg, Colonial paid around five million dollars (€4.1 million) ransom to stop the attack on its Pipeline that brought the fuel supply in the United States to the brink of collapse.
- Connections to Russia?
In a statement published on Darknet – the part of the Internet that is not accessible to ordinary users – Darkside stresses that it has “no political agenda” and no ties to governments. The only goal is to make money.
In doing so, the criminals apparently want to give themselves a humane touch: it is not a matter of creating social problems through attacks, they stress: therefore, only companies that are guaranteed to raise the ransom would be attacked.
US investigators suspect that Darkside is based in Russia. Experts point out, among other things, that so far only Western companies have apparently been attacked with Darkside software and no Russian ones.
“Responsible ‘actors’ in Russia”
US President Joe Biden recently stated that there was no evidence that the Russian government was responsible for the attack on Colonial Pipeline. However, there are indications that the responsible “actors” are in Russia and that the malware comes from there.
Moscow, for its part, rejected all allegations of involvement or backing for the attack. Russia does not carry out” malicious ” activities on the internet, the Russian embassy in the USA said.
- Darkside-Server probably switched off
The server used by the supposedly responsible hacker group has apparently been shut down by unknown parties. The US security firm Recorded Future stated that the operator of the Darkside blackmail trojan had stated in a post that he had lost access to the servers. Among others, the blog of the group and the payment server are affected. Also, cryptocurrency captured by extortion was lost.